Quantum Readiness Assessment
For Chief Information Security Officers (CISOs) and security leaders, ensuring…
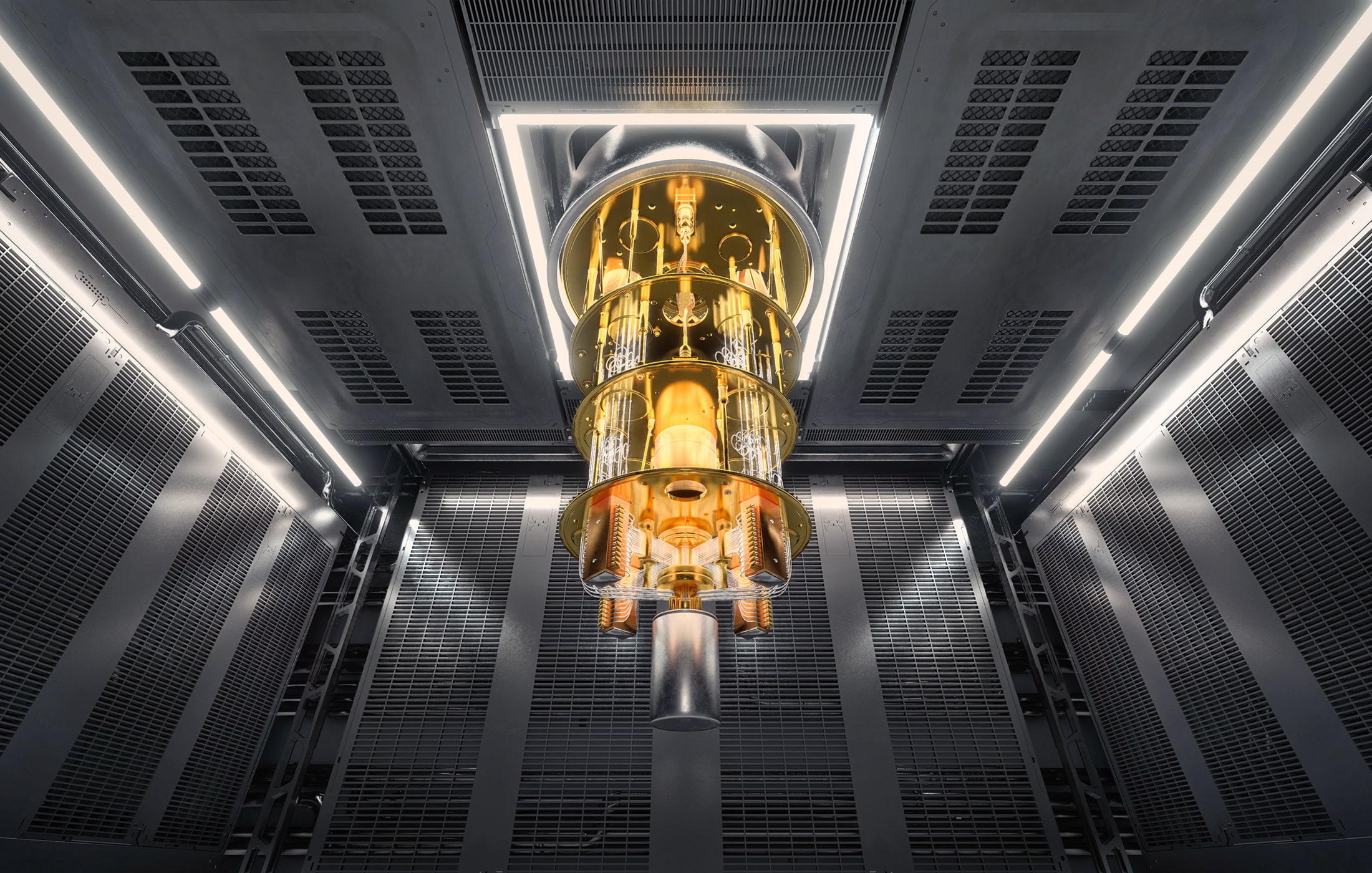
The Enormous Energy Cost of Breaking RSA‑2048 with Quantum Computers
Quantum computers promise to crack encryption schemes that are effectively…
Breaking RSA Encryption: Quantum Hype Meets Reality (2022-2025)
In late 2022, a remarkable claim jolted the cryptography and quantum computing…
Post-Quantum Cryptography (PQC) Standardization - 2025 Update
The Quantum Threat and Need for PQC Modern public-key cryptography,…
NIST PQC Security Strength Categories (1–5) Explained
Understanding NIST’s PQC Security Categories As part of its post-quantum…
Quantum Readiness: What Crypto Exchanges Should Do Today
The Quantum Threat: Why Exchanges Can’t Ignore It Crypto exchanges sit at a…
Physics at the Heart of the New Cold War
Introduction In the 21st century, cutting-edge physics has moved from the…
Hybrid Cryptography for the Post-Quantum Era
Introduction Quantum computers threaten to upend the cryptographic…
Quantum Key Distribution (QKD) 101: A Guide for Cybersecurity Professionals
Quantum Key Distribution (QKD) is a cutting-edge security technology that…
Adiabatic Quantum (AQC) and Cyber (2024 Update)
Introduction Quantum computing promises to solve certain classes of problems…